Have you ever thought about measuring the Internet in terms if malware per minute? Me neither, but someone has and it makes for uncomfortable reading if you are a Microsoft Windows user.
How fast is the Internet? It depends on the metric being used, of course, but one new report published this week has an interesting new take on this old question. How does four malware apps per minute grab you? According to German security vendor G Data , the number of new malware applications has already hit a record for the first half of the year with more than a million recorded in just six months alone.
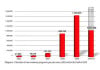
The 1,017,208 malware programs represent an increase of 50 percent compared to the same period last year, and security experts are now confidently predicting that by the end of 2010 we will have witnessed more than two million of them. Of that million or so malwares, 99.4 percent was written to target the Windows Operating System. Breaking it down further, 42.6 percent were Trojans, with downloaders and droppers representing 20.3 percent. Backdoor malware code makes up just 12 percent of the total, while worms represented just 5.27 percent of the total.
"The current numbers are alarming. The malware industry has published nearly four new viruses per minute in the first half of the year" so says Eddy Willems, G Data’s Security Evangelist, who added that the attackers are mainly targeting social networks and their members as they represent "especially profitable targets because of their high number and their interlinked nature".
DaniWeb asked Mr Willems why the number of new malware apps was so high? "Because it’s an easy and profitable business" was the answer, with Mr Willems insisting that the risk of finding the hackers responsible is relatively very low. "Cybercrime is very high and mostly coming from regions as Russia, India, South-America" he told us, adding "where people generally don’t earn too much in comparison with the rest of the world". You might be excused for thinking that such high numbers of new malware applications must mean that security vendors are doing a bad job and this is being exploited by the bad guys. But actually it is more likely to be exactly the opposite, in fact, with security vendors doing such a good job of identifying and countering malware that the rogue coders are forced to churn out new versions in ever increasing number and ever increasingly faster for good measure. Eddy Willems told DaniWeb that "security vendors are doing a good job as we can still counter all of these malware ASAP when released by use of the reactive and proactive solutions".
Of course, there is also an argument to be had which says that if security vendors were doing a really good job then no malware would be able to execute a payload and the bad guys would not be making any money. If that were truly the case, then surely we would be seeing criminal gangs giving up and turning their attention to something else. The sheer scale of the increase in new malware code that is being released would tend to suggest that this is not the case, and that there is still plenty of money to be made with malware.
Unless you are a Mac user , that is, as these figures point to you not being of any real value to Internet villains at all.