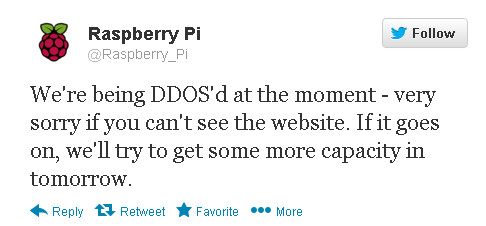
The news wires have been buzzing over the weekend after it emerged that the Raspberry Pi website had been hit by a 'million zombie' Distributed Denial of Service (DDoS) attack during the week. Although the outage was relatively brief, with the Raspberry Pi Foundation admitting the attack with a Twitter message that stated "We're being DDoS'd at the moment—very sorry if you can't see the website" and continued "If it goes on, we'll try to get some more capacity in tomorrow". The attack meant that parts of the site were offline for e a few hours while others were very slow and intermittent.
 Forget the media obsession with that 'million zombies' headline, which seems to have come about after someone posted a statement claiming the attack took the form of a significant SYN flood from a botnet with about a million nodes. To be honest, botnets are out there for hire by people who want to launch such attacks and a million nodes may be on the large side but it's not particularly uncommon these days. What is uncommon, or so you might think, is for a DDoS attack to target something as harmless as Raspberry Pi in the overall scheme of things; a charitable foundation no less. The general perception is that hacktivism rules when it comes to DDoS attacks, and that the victims are mainly big business and political targets. That perception is, sadly, rather unfounded.
Forget the media obsession with that 'million zombies' headline, which seems to have come about after someone posted a statement claiming the attack took the form of a significant SYN flood from a botnet with about a million nodes. To be honest, botnets are out there for hire by people who want to launch such attacks and a million nodes may be on the large side but it's not particularly uncommon these days. What is uncommon, or so you might think, is for a DDoS attack to target something as harmless as Raspberry Pi in the overall scheme of things; a charitable foundation no less. The general perception is that hacktivism rules when it comes to DDoS attacks, and that the victims are mainly big business and political targets. That perception is, sadly, rather unfounded.
Sure, the Anonymous attacks with a political agenda tend to grab the headlines but that does not mean they are the norm. The truth of the matter is that greed rather than any political or hacktivist agenda is behind far more DDoS attacks. The most common motive is financial blackmail, pure and simple. We take down your site briefly to prove it can be done, you pay us an 'insurance fee' to ensure we don't do it again for a longer period and put you out of business. That's the criminal thinking behind many DDoS attacks, although it is not clear if that's the case with the Raspberry Pi targeting this last week. I would, however, be very surprised indeed if this had the fingerprints of Anonymous upon it as it would serve no activist (or 'lulz') purpose whatsoever. The Raspberry Pi Foundation admits that it has been hit a couple of times in a couple of days, which could point to the blackmail theory and a demand coming soon.
One thing worth noting though, is that this is not the first time that Raspberry Pi has been the victim of a DDoS attack. A bit of research on the Raspberry Pi forums found this from June 14th 2012:
You might have noticed that this site has been up and down over the last 24 hours. We're undergoing a DDoS attack - depending on how long it continues, we may be spending some time later on sticking Cloudflare in front of the site, but for now we're crossing our fingers and hoping that whoever is pointing their botnet at us will get bored and wander off. It's a big botnet. We've been seeing a DDoS that's roughly 110Mbps of SYN packets (307kps) to port 80. There's nothing terribly sensible our buddies at Mythic Beasts, who host this site, can do; it's pegged one CPU at 100% just managing the firewall connection state, and Apache has (unsurprisingly) run out of connections when it's at its worst. We think that the Ethernet wire is also full. Gigabit Ethernet pads to 512 bytes, which is roughly 1.2Gbps on a 1Gbps link. It's frustrating, but we're not suicidal (yet); for now we're taking the downtime to do the admin we need to do and steam through some email. I'll be posting regular updates on Twitter - please discuss below what sort of twonk thinks that DDoSing a charity is a smart thing to do.
A follow up posting from the same member of staff claimed:
It's either someone doing it for the lulz, someone we've banned for being an idiot, or someone who's taken offence at something we've said at some point - you know how people can get about favourite platforms/languages/OSes. Or it could be a blackmail thing (lots of these are, and this one does seem pretty large and well organised) - we haven't had any email to that effect, though. (Unless they mailed info@, which folder is currently several thousand deep in unread mail.)
And then, just eight days later, there was another posting about Raspberry Pi being targeted by the DDoS crowd:
Some complete idiot is doing a distributed denial-of-service attack (DDoS attack) on Sam's Raspbmc website and server. They have knocked out his website and servers and that stops the RC3 from installing. It started yesterday evening and that complete idiot is doing it again this evening. The good news is that his exams are now over and he has started work on RC4. I have found the RC3 to very good especially the CEC support that allows you to control Raspbmc with your TV remote. I managed to grab a copy very early this morning. Sorry you won't be able get RC3 until the attack stops or until SAM finds a fix because the installer won't work as it depends on his servers being up. Sam thanks for everything you have done on this. Raspbmc is very impressive.
The Raspberry Pi Foundation talked about using a dedicated DDoS mitigation service to reduce the chances of being taken down again following the 2012 attacks, but from what has happened this last week that would not appear to have been done. I understand that some mitigation has been provided by way implementing SYN cookies, but this is patently not enough. It's not clear if the same person or group is behind the current DDoS attack as was responsible for those a year ago, or if any blackmail demands were ever received at the time.
