No more shortcuts for hackers - that's the word from Microsoft, which plans to release a patch today that the company says will fix a security loophole. The issue is tied to the way the Windows OS handles shortcuts, or .lnk files, or as Microsoft explains it in the official security advisory : "The vulnerability exists because Windows incorrectly parses shortcuts in such a way that malicious code may be executed when the icon of a specially crafted shortcut is displayed. This vulnerability can be exploited locally through a malicious USB drive, or remotely via network shares and WebDAV. An exploit can also be included in specific document types that support embedded shortcuts."
In other words, all it takes is viewing the contents of a USB drive to embed a malicious shortcut in your system.
Microsoft says the loophole is present in Windows XP Service Pack 3 and x64 Service Pack 2, right on up through Windows 7, including Windows Server 2003 and 2008. Consumers were first notified of the problem in the middle of July, along with detailed directions for a temporary workaround . Company managers say that in the interim they've seen an increase in attempts to exploit the vulnerability, prompting today's "out of band" release of the patch (out of band is Redmond-speak for outside the regular monthly update schedule).
Microsoft's Holly Stewart says that Malware in the Sality family , especially Sality.AT, have been among the most active and "virulent" of those using the shortcut backdoor:
"It is known to infect other files (making full removal after infection challenging), copy itself to removable media, disable security, and then download other malware. It is also a very large family—one of the most prevalent families this year. After the inclusion of the .LNK vector, the numbers of machines seeing attack attempts combining malicious .LNKs and Sality.AT soon surpassed the numbers we saw with Stuxnet. We know that it is only a matter of time before more families pick up the technique."
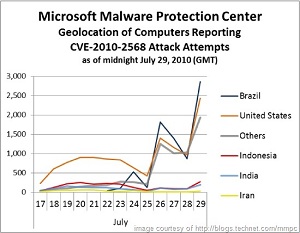
Stewart and Microsoft report that most of the computers reporting attack attempts through last week were located in Brazil, but the United States was a very close second.
Windows users with Windows Update turned on can expect to see the patch hit their systems around 1 p.m. Eastern Time today.
Image courtesy of Microsoft at http://blogs.technet.com/mmpc