Menu
Menu
DaniWeb
Log In
Sign Up
Read
Contribute
Meet
Search
Search
About 1,000 results for
security
- Page 1
Best Approach for Starting a Linux-Based Home Automation Pro
Hardware and Software
Linux and Unix
2 Weeks Ago
by Aria James
… working with sensors and relays easier under Linux and common
security
or performance pitfalls I should keep in mind when exposing…
Re: Screaming Frog Comparisons
Digital Media
Digital Marketing
Search Engine Strategies
1 Week Ago
by toneewa
…the filtering option tabs. E.g., internal, external,
security
, canonicals, page titles, url, etc... The labels …quot;. Removed is URLs in filter (internal, external,
security
, canonicals, page titles, url, etc...) for previous crawl…, but not in the filter (internal, external,
security
, canonicals, page titles, url, etc...) for current crawl…
Re: What are "Other agent type" Googlebot types in GSC crawl stats?
Digital Media
Digital Marketing
Search Engine Strategies
2 Weeks Ago
by bijutoha
…, my first thought is usually a manual action or a
security
issue from Google. Have you had a chance to check… your GSC under **Manual actions** and **
Security
issues** yet? That's usually where Google will tell you…
Re: What are "Other agent type" Googlebot types in GSC crawl stats?
Digital Media
Digital Marketing
Search Engine Strategies
2 Weeks Ago
by bijutoha
…, that's genuinely good news about no manual actions or
security
issues, at least that rules out the scariest stuff! But…
Re: What are "Other agent type" Googlebot types in GSC crawl stats?
Digital Media
Digital Marketing
Search Engine Strategies
2 Weeks Ago
by Dani
No manual actions or
security
issues.
Re: Securing Customer Data: An Essential Cybersecurity Handbook
Hardware and Software
Information Security
4 Weeks Ago
by graceweb
Hey Bam_391, Thanks for putting this together, really thorough breakdown. I think your point about regular employee training is especially important. Even with the best technical safeguards, a single phishing click can cause major issues. Curious if you have any thoughts on balancing strict access controls with usability, especially in smaller …
Re: Securing Customer Data: An Essential Cybersecurity Handbook
Hardware and Software
Information Security
1 Week Ago
by WilliamOG
Basically: patch your stuff, lock your doors, and stop clicking shady emails. Got it.
Re: Best Approach for Starting a Linux-Based Home Automation Pro
Hardware and Software
Linux and Unix
2 Weeks Ago
by trcooke
Hello, I'd probably start with an open source off the shelf solution such as https://www.home-assistant.io/ There are tutorials on their site that cover installation onto a raspberry pi so you should be able to get to and running fairly quickly. It sounds like a fun project so please do let us know how you get on.
Re: Best Approach for Starting a Linux-Based Home Automation Pro
Hardware and Software
Linux and Unix
2 Weeks Ago
by Dani
What about using something like [IFTTT](https://ifttt.com/)?
Re: Best Approach for Starting a Linux-Based Home Automation Pro
Hardware and Software
Linux and Unix
2 Weeks Ago
by trcooke
Oh yes IFTTT definitely a good shout. I've had some success with it in the past. When our son was a baby we had real trouble keeping his room warm in the winter because the upstairs thermostat was out in the hall which was nice and toasty from all the heat of the house rising to meet it, while his bedroom with the door closed was cold. I …
Re: Best Approach for Starting a Linux-Based Home Automation Pro
Hardware and Software
Linux and Unix
2 Weeks Ago
by Dani
I assume your son is no longer a baby, but nowadays you can get Nest temperature sensors to put in different areas of your home. You can officially tell Nest to control the HVAC based on the temperature of the family room during the day and the temperature of the bedroom at night, for example.
Re: Best Approach for Starting a Linux-Based Home Automation Pro
Hardware and Software
Linux and Unix
2 Weeks Ago
by trcooke
Indeed not. He's 7 now. Yes you can get those free standing mounts, but I don't have any. My thermostats are wired into the wall. It'd be cool if you could just pop them off the wall and stick them on a stand anywhere you like, but alas you cannot.
Re: Best Approach for Starting a Linux-Based Home Automation Pro
Hardware and Software
Linux and Unix
2 Weeks Ago
by Dani
Huh? I'm referring to [these](https://www.amazon.com/Google-Nest-Temperature-Sensor-Pack/dp/B0D5J7G9J2/ref=asc_df_B0D5J7G9J2?mcid=eae5a49f4a903a8db2d8e80887222083&hvocijid=7880327826579386076-B0D5J7G9J2-&hvexpln=73&tag=hyprod-20&linkCode=df0&hvadid=721245378154&hvpos=&hvnetw=g&hvrand=7880327826579386076&hvpone=&…
Re: Best Approach for Starting a Linux-Based Home Automation Pro
Hardware and Software
Linux and Unix
2 Weeks Ago
by trcooke
Oh I have not seen those before... interesting. I was thinking of this 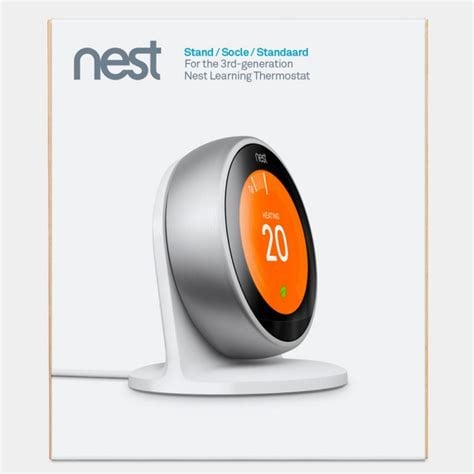
Re: Best Approach for Starting a Linux-Based Home Automation Pro
Hardware and Software
Linux and Unix
2 Weeks Ago
by trcooke
Apparently not available in the UK. Although Amazon UK are selling them and there are lots of angry reviews left.
Re: Best Approach for Starting a Linux-Based Home Automation Pro
Hardware and Software
Linux and Unix
2 Weeks Ago
by Dani
How can you bear to live in such an uncivilized country?!
Re: Best Approach for Starting a Linux-Based Home Automation Pro
Hardware and Software
Linux and Unix
2 Weeks Ago
by Dani
P.S. Here in the US, our Nests are directly connected to the HVAC system hardwired in the wall, so they aren’t movable at all.
Re: 💻 What’s the First App You Install on a Fresh Windows Machine?
Hardware and Software
Microsoft Windows
2 Weeks Ago
by Yrth
> Jim, I have not used Windows in a very, very long time, but can you not configure Windows to store My Documents on D? I'm quite sure that you can, if I remember correctly? > > https://superuser.com/questions/1725456/wha-cant-i-move-my-documents-folder You can't, directly, but you can cheat, of course. Put your documents directory …
Re: 💻 What’s the First App You Install on a Fresh Windows Machine?
Hardware and Software
Microsoft Windows
2 Weeks Ago
by Reverend Jim
That's exactly what I did except I used sysinternals junction.exe. This still leaves things screwed up in that the address bar may still show you in OneDrive even though you are saving to the junction point.
Re: 💻 What’s the First App You Install on a Fresh Windows Machine?
Hardware and Software
Microsoft Windows
2 Weeks Ago
by donnamitch
Hello
Re: Best Approach for Starting a Linux-Based Home Automation Pro
Hardware and Software
Linux and Unix
1 Week Ago
by WilliamOG
Great project idea, and you're already ahead with your electronics background. For the OS, Raspberry Pi OS Lite is a solid starting point—lightweight, well-supported, and ideal for headless setups. If you want something even more stripped down, check out DietPi or Ubuntu Server for Pi, but the trade-off is slightly less community support.
Re: Cannot run exe from asp.net
Programming
Web Development
1 Month Ago
by lennyli
… you're trying to do is mostly blocked by modern
security
rules — for good reasons. Here's the breakdown: &… on someone’s computer directly — it’s a huge
security
risk. > > Why your webpage button might…of another computer involves several technical aspects, including networking,
security
, and user interface design. Below, I’ll outline a…
Re: Cannot run exe from asp.net
Programming
Web Development
1 Month Ago
by Neil_brown001
… you're trying to do is mostly blocked by modern
security
rules — for good reasons. Here's the breakdown: Running a… apps on someone’s computer directly — it’s a huge
security
risk. Why your webpage button might not be working The…
Cannot run exe from asp.net
Programming
Web Development
2 Months Ago
by lennyli
… did not run even when i set it to have
security
permissions so let everyone have all rights. im a little…
Re: Cannot run exe from asp.net
Programming
Web Development
2 Months Ago
by lennyli
> Are you sure IIS is configured to allow running external scripts? The document folder and asp file has
security
permission set to ALL rights for 'everyone'. In IIS, under handler mappings for .asp files, under request restriction/access, script was chosen (not execute) for feature permissions, all 'read' 'script' 'execute' are chosen
Re: Cannot run exe from asp.net
Programming
Web Development
1 Month Ago
by gediminas.bukauskas.7
Pritaeas answered the question: normal WEB
security
settings forbids launching executables on a client machine. The only legal workaround is to create windows service (daemon in Linux environment), install it on client machine and listen for some commands coming from server over WEB sockets.
Re: Cannot run exe from asp.net
Programming
Web Development
1 Month Ago
by lennyli
> Pritaeas answered the question: normal WEB
security
settings forbids launching executables on a client machine. The only …
💻 What’s the First App You Install on a Fresh Windows Machine?
Hardware and Software
Microsoft Windows
1 Month Ago
by asadalikhan
…: Your favorite browser (Chrome, Firefox, Brave?) A trusted antivirus or
security
tool An essential productivity app Something for customization or system…
Re: 💻 What’s the First App You Install on a Fresh Windows Machine?
Hardware and Software
Microsoft Windows
1 Month Ago
by dnBunnie
the app "Everything" after Comodo Internet
security
Re: 💻 What’s the First App You Install on a Fresh Windows Machine?
Hardware and Software
Microsoft Windows
1 Month Ago
by Reverend Jim
I agree. [Everything](https://www.voidtools.com/) is always a definite install after imaging. It's something that should have been built into Windows. I've never found the need for any
security
software other than what comes with Windows.
1
2
3
17
Next
Last
Search
Search
Forums
Forum Index
Hardware/Software
Recommended Topics
Programming
Recommended Topics
Digital Media
Recommended Topics
Community Center
Recommended Topics
Latest Content
Newest Topics
Latest Topics
Latest Posts
Latest Comments
Top Tags
Topics Feed
Social
Top Members
Meet People
Community Functions
DaniWeb Premium
Newsletter Archive
Markdown Syntax
Community Rules
Developer APIs
Connect API
Forum API Docs
Tools
Backlink Auditor
Legal
Terms of Service
Privacy Policy
FAQ
About Us
Advertise
Contact Us
© 2025 DaniWeb® LLC