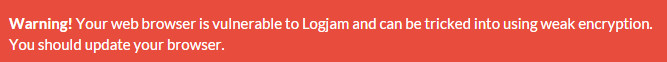
Another month, another flaw related to the historical US export restrictions on cryptography; this time in the form of LogJam. It hits SSL 3.0 and TLS 1.0 which supported reduced-strength DHE_EXPORT ciphersuites, restricted to primes no longer than 512 bits, meaning that a man-in-the-middle attack is possible to force the usage of the lower export strength cipher without the user being aware and which impacts something like eight per cent of the top one million web domains and all the major web browser clients. Well almost, because Internet Explorer has already been patched (nice one Microsoft) with Firefox expected to follow soon and Chrome after that although time scales are not yet confirmed. You can confirm if your browser client has been updated yet by visiting https://weakdh.org
I'm not going to go into huge depth about the bug itself here, mainly because it's been covered very well by lots of places already. If you have a technical bent, and as a DaniWeb member I'm guessing that's pretty likely, then I'd suggest reading the original disclosure paper itself which can be found as a PDF here.
Here's the abstract for a taster of what you will find:
We investigate the security of Diffie-Hellman key exchange as used in popular Internet protocols and find it to be less secure than widely believed. First, we present a novel flaw in TLS that allows a man-in-the-middle to downgrade connections to “export-grade” Diffie-Hellman. To carry out this attack, we implement the number field sieve discrete log algorithm. After a week-long precomputation for a specified 512-bit group, we can compute arbitrary discrete logs in this group in minutes. We find that 82% of vulnerable servers use a single 512-bit group, allowing us to compromise connections to 7% of Alexa Top Million HTTPS sites. In response, major browsers are being changed to reject short groups. We go on to consider Diffie-Hellman with 768- and 1024-bit groups. A small number of fixed or standardized groups are in use by millions of TLS, SSH, and VPN servers. Performing precomputations on a few of these groups would allow a passive eavesdropper to decrypt a large fraction of Internet traffic. In the 1024-bit case, we estimate that such computations are plausible given nation-state resources, and a close reading of published NSA leaks shows that the agency’s attacks on VPNs are consistent with having achieved such a break. We conclude that moving to stronger key exchange methods should be a priority for the Internet community.
So, what do security experts have to say about LogJam? I've been out and about and have collated the following comments which help put things into context:
Ross Brewer, vice president at LogRhythm, says "Currently it feels like a day doesn’t go by without an organisation being hacked, or a new security vulnerability being revealed. Over the last year or so we’ve seen a few serious flaws exposed and it’s likely we’ll see many more as the internet gets older and hackers get better at finding and exploiting cracks that have appeared. However, some threats are more serious than others and, while it pays to make people aware of all of them, we need to try and avoid causing mass hysteria each time one emerges. The fact that LogJam can only be exploited when hackers and targets are on the same network, as well as patches being imminent, means that hype around it is likely to be a bit of a storm in a tea cup. Organisations should, however, use flaws like this as an excuse to give themselves a security health-check. While the fact that someone has to be on the same network to take advantage of the flaw may see many breathe a sigh of relief, they do have to ask themselves one question – would we know if they are and taking advantage? With an increase in remote working, as well as a few high profile breaches perpetrated by a malicious insider, no-one should be resting on their laurels quite yet. We’ve seen countless cyber hacks take months, or even years in some cases, to be identified and remediated, so everyone should really be double-checking they’re clean. No business is safe today and trying to prevent attacks is becoming almost pointless. If a hacker wants to get in badly enough, they’ll happily spend some time by-passing even the best firewalls and intrusion detection systems. Given this, organisations need to shift their focus from trying to stop them getting in, to making sure that, when they do, they can get them out as quickly as possible. Businesses now need to have the necessary security intelligence in place, to enable them to detect and respond to threats in hours and minutes – rather than months and days – to be sure they can limit any damage. With flaws like LogJam being identified with increasing frequency, the only real way to know you’re safe is to know you can stop an attack in its tracks as soon as it gets going."
Meanwhile, here's what Ivan Ristic (director of application security research at Qualys) has to say "LogJam, the new attack on weak Diffie-Hellman (DH) parameters is yet another reminder that supporting obsolete cryptography is never a good idea. Even though TLS provides a negotiation mechanism that should, in theory, enable modern clients to communicate using only strong security, in practice there are ways to abuse either the clients or the protocol and perform downgrade attacks. Diffie-Hellman key exchange strength is a relatively obscure aspect of TLS protocol configuration. Until recently, most web servers didn't even have an ability to tune this setting, and some servers don't even today. That wouldn't be a problem, except that most servers default to insecure values. LogJam affects only incorrectly configured SSL/TLS servers so those who have followed best practices aren't using any of the vulnerable cryptography ,and need not make any changes to mitigate LogJam. In addition, for performance reasons, well-tuned sites prefer key exchanges based on Elliptic Curve cryptography, avoiding problems with DH altogether."
Kevin Bocek, vice president of security strategy and threat intelligence at Venafi, says "After FREAK was discovered a few months back, LogJam certainly comes as no surprise. Weakened encryption protocols like this one with Diffie-Hellman are a disaster waiting to happen as cyber criminals will prey on these vulnerabilities and spy on encrypted connections used by thousands of HTTPS sites and email servers. Heartbleed, LogJam, FREAK, Superfish and so many other examples reinforce that there's too much blind trust when it comes to SSL/TLS, certificates and trust. And I have no doubt that we'll continue to find many more protocol, crypto, and certificate vulnerabilities out there lurking. SSL/TLS and certificates are the foundation of security on the Internet. The lesson is the same: SSL/TLS keys, and certificates are too important to be treated with the same blind trust. With more sites using SSL/TLS keys and certificates, the target is getting bigger for bad guys. Their interest in intercepting encrypted traffic, spoofing trusted sites, or hiding in encryption is only growing and many out there predict that a crypytoapocalypse is on the horizon. IT security pros need to know what type of crypto is being used and where their certificates are located and if they are up to date. The prevalence of vulnerabilities and attacks on SSL/TLS and certificates have shown us that this problem is not going away anytime soon and therefore we must be vigilant in protecting the foundation of trust on the Internet."