An investigation by UKFast has revealed that it is possible to build a super-cracker computer for around the same price as your average low-spec budget desktop PC. Yet unlike your average budget PC, it is claimed that this cybercrime dream machine is capable of processing billions of password combinations per second.
Investigators from UKFast built this low budget but high powered password cracker using two readily available graphics cards to provide the firepower necessary to drive the processing of password combos at such an alarmingly fast rate.
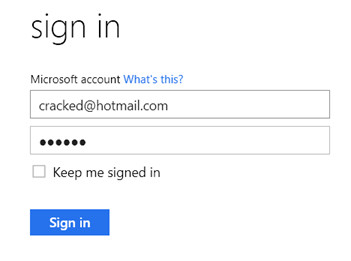
Costing less than £400 ($620) this particular machine was built by the security team at UKFast and could crack a 'complex password' of six random alpha-numerical and special characters in under 90 seconds. Bog standard six character passwords were dead in under a second. Obviously, the longer the password so the longer the time to crack becomes providing that you stick to the non-dictionary and mixed alpha-numerical and special character construction method. Jump into the realms of the 15 character truly random password, which is my own personal baseline these days, and to be honest it's hardly worthwhile for the bad guys to bother with.
So why does this machine deserve the title of 'super cracker' then? Well that's simple and twofold: firstly, the vast majority of folk out there do not have long and complex passwords and many sites and services still restrict the maximum length of a password and disallow the use of special characters; secondly, these are exactly the kind of computers being put to use by the bad guys in decoding those stolen databases of encrypted (hashed but not salted) usernames and passwords that you read about in the news.
Stuart Coulson, who is head of the security team that built the budget beast, explains that it's "the architecture of the graphics cards" that provides the firepower needed to complete repetitive tasks such as brute force cracking passwords at lower cost and faster speed. "The closest alternative that has this level of cracking power would cost more than £600 just for the graphics card" Coulson continues, concluding "the fact that this level of power is so readily available to cyber criminals highlights the importance of long and complicated passwords and for businesses to use strong encryption algorithms for their data.”
