An in-the-wild exploit targeting a vulnerability with Java 7 has led to security experts the world over warning users to disable the Java plug-in for their browser clients at the very least, and preferably uninstall Java altogether. The CVE-2012-4681 vulnerability, comprising two flaws, along with a couple of other 'related vulnerabilities' has now been patched by Oracle which strongly recommends users apply the updates as soon as possible. Security Explorations, the Polish security company that first notified Oracle about the vulnerabilities many weeks ago, is less convinced.
 It would appear that the company has found another vulnerability in the newly patched version of Java 7. Adam Gowdiak, the Security Explorations CEO, has claimed that the new vulnerability enables a 'complete JVM sandbox bypass' within the latest Java SE 7 update 7 environment. Security experts seem to think that the reason why Oracle managed to turn around such a quick patch, within a few days of the insecurity story breaking across the Internet, is that it blocked the route to the vulnerability in order to prevent exploitation rather than actually remove the vulnerability itself. What Security Explorations seem to have discovered is a way to route around that roadblock and arrive at the same vulnerability, although it should be pointed out that there are no suggestions of any new exploits being in the wild at this time.
It would appear that the company has found another vulnerability in the newly patched version of Java 7. Adam Gowdiak, the Security Explorations CEO, has claimed that the new vulnerability enables a 'complete JVM sandbox bypass' within the latest Java SE 7 update 7 environment. Security experts seem to think that the reason why Oracle managed to turn around such a quick patch, within a few days of the insecurity story breaking across the Internet, is that it blocked the route to the vulnerability in order to prevent exploitation rather than actually remove the vulnerability itself. What Security Explorations seem to have discovered is a way to route around that roadblock and arrive at the same vulnerability, although it should be pointed out that there are no suggestions of any new exploits being in the wild at this time.
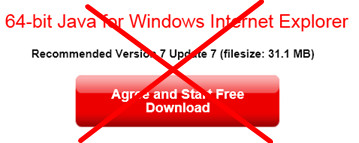
Some security commentators are recommending that users roll back to Java 6 which, with it's reduced feature set compared to Java 7, is not susceptible to the same vulnerability. However, given the way that this whole insecurity story is panning out so far I think that the original advice to disable any browser Java plug-ins or uninstall Java completely is a more appropriate security measure. The possibility that the bad guys might be able to bypass the Java security sandbox and execute malicious code on a target machine is just too big a risk to take.
Oracle has stated that it is analysing the Security Exploration's vulnerability report and proof of concept code, but has yet to confirm that the flaw remains. With the next Critical Patch Update for Java not scheduled until October 16th, Oracle needs to get on the case and either confirm or deny this ASAP. If the researchers turn out to be right, as they were with the original vulnerability report, then Oracle will need to produce yet another out of band update as soon as possible if it is to prevent even further reputational damage.
