Earlier this week, an iPhone jailbreaking guru called pod2g revealed how even the very latest beta versions of iOS 6 cannot prevent the iPhone from being vulnerable to SMS text message spoofing. This technique is often employed by spammers and scammers alike when targeting the smartphone user in order to get them to click on a link or otherwise responds to what appears to be a message from a trusted source.
 Technically it's about as simple as it gets: all the would-be spoofer needs to do is change the User Data Header indicator within the Protocol Description Unit format that text messages get converted to. By changing the reply to field of the message, the recipient will end up (obviously) replying to that number but has no way of knowing it as the number from the original SMS text isn't displayed on the iPhone. Writing about the exploit, pod2g argues that the ideal solution would be for the recipient to "see the original phone number and the reply-to one" but that doesn't happen on the iPhone.
Technically it's about as simple as it gets: all the would-be spoofer needs to do is change the User Data Header indicator within the Protocol Description Unit format that text messages get converted to. By changing the reply to field of the message, the recipient will end up (obviously) replying to that number but has no way of knowing it as the number from the original SMS text isn't displayed on the iPhone. Writing about the exploit, pod2g argues that the ideal solution would be for the recipient to "see the original phone number and the reply-to one" but that doesn't happen on the iPhone.
This, as is always the case when Apple or iPhone is mentioned in such a story, kicked off a huge number of follow-on stories about how insecure the iPhone is. The inevitable comment threads then appeared either suggesting that people switch to Android handsets instead or that the original story was a big pile of pants, depending upon the fanboy status of the poster of course.
The truth of the matter is that this is not an Apple, an iPhone or an iOS issue at all: it's a SMS issue. The entire SMS text message system has pretty much nothing by way of useful authenticity checking along the way built in, it was never developed as a 'secure' messaging system. You only have to go Google for SMS spoofing sites on the web to discover that there are plenty which provide the service, either for free or for a fee, and the recipient phone handset matters not one jot. As long as the handset itself allows that UDH indicator for the alternative reply-to address to be changed then all bets are off.
Now I have not always been the most supportive of Apple when they reply to stories surrounding security holes within their products or services, as all too often that response tends to consist of either an ostrich impression, a straight denial or silence. On this occasion, however, Apple has not been silent and not denied that SMS on an iPhone can be spoofed. It has, instead, via a response posted to Engadget quite clearly stated that: 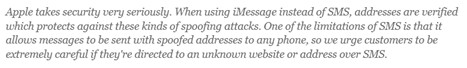
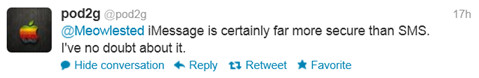
So there you have it, use iMessage instead of SMS on an iPhone if you want to avoid the spoofing issue. Even the jailbreaker who kicked this whole shebang off, pod2g, agrees and has Tweeted "iMessage is certainly far more secure than SMS. I've no doubt about it". Of course, Apple could do something about the way the iPhone displays originating and reply-to numbers in text messages, but spoofing has been around since the dawn of email and the dawn of SMS truth be told. It's nothing new, and the best way to protect against it is user vigilance. Either that, or buy all your mates an iPhone so they can start using iMessage as well...
