pliz i need help in my assignment who it in this photo
doushka6300 0 Newbie Poster
Recommended Answers
Jump to PostThe terms of use for these forums is that we don't do your homework for you. Make a reasonable attempt and we will try to help you understand where you went wrong, but YOU have to start the process.
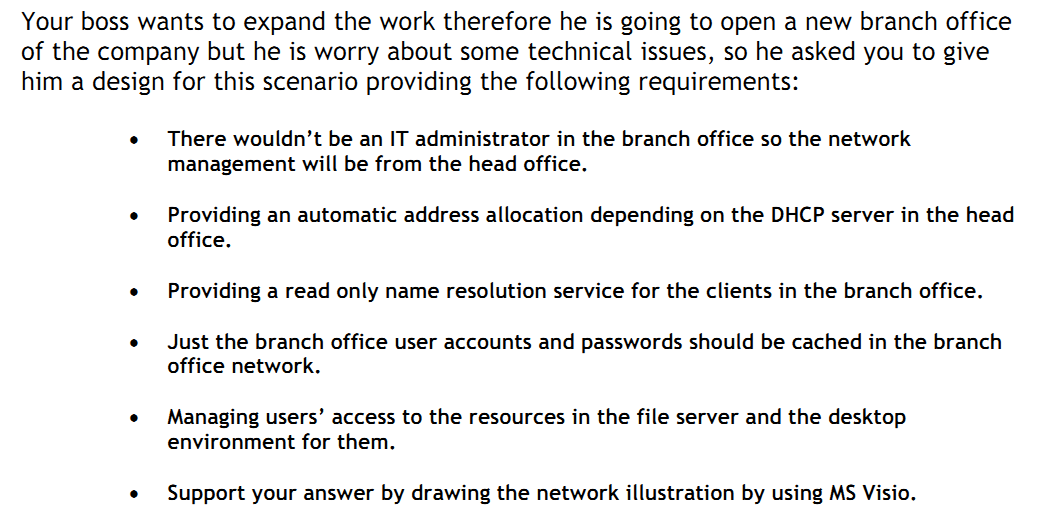
Jump to PostFirst, take each point that he wants you to consider, and state what that means to you in simple terms, as well as how you migh accomplish that.
Jump to PostHow do you address the first point? Think about the tools needed for an IT administrator to manage a remote office.
the other questions are giving you clues as to where to place the server roles. If you arent familiar with the roles, the placement is not obvious.
The second …
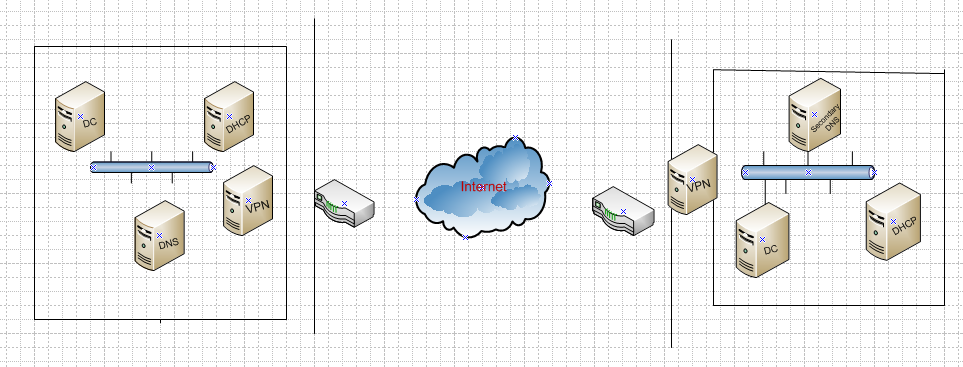
Jump to PostOk so some of the roles you have placed seem to be correct, but the bullet points are specific about requirements, specifically bullets 2-5, that you dont show in your diagram.
Your second bullet is referring to a DHCP solution that depends on the head office. You listed two DHCP …
All 14 Replies
rubberman 1,355 Nearly a Posting Virtuoso Featured Poster
doushka6300 0 Newbie Poster
rubberman 1,355 Nearly a Posting Virtuoso Featured Poster
doushka6300 0 Newbie Poster
JorgeM 958 Problem Solver Team Colleague Featured Poster
doushka6300 0 Newbie Poster
JorgeM 958 Problem Solver Team Colleague Featured Poster
doushka6300 0 Newbie Poster
JorgeM 958 Problem Solver Team Colleague Featured Poster
doushka6300 0 Newbie Poster
JorgeM 958 Problem Solver Team Colleague Featured Poster
doushka6300 0 Newbie Poster
JorgeM 958 Problem Solver Team Colleague Featured Poster
doushka6300 0 Newbie Poster
Be a part of the DaniWeb community
We're a friendly, industry-focused community of developers, IT pros, digital marketers, and technology enthusiasts meeting, networking, learning, and sharing knowledge.